Dr. Kemal Akkaya E-mail: [email protected]
description
Transcript of Dr. Kemal Akkaya E-mail: [email protected]

Wireless & Network Security 1 Kemal Akkaya
Department of Computer ScienceSouthern Illinois University Carbondale
CS 591 – Wireless & Network SecurityLecture 12: Trust
Dr. Kemal AkkayaE-mail: [email protected]

Wireless & Network Security 2 Kemal Akkaya
TrustTrust Definition:
The belief that an entity is capable of acting reliably, dependably, and securely in a particular case
A well studied concept in sociology and psychology. Need for trust
Traditional schemes focus on preventing attackers from entering the network through security protocols.
Those schemes, however, are not effective when: Malicious nodes have gained access to the network Some nodes in the network have been compromised
Trust function: Provide an incentive for good behavior. Provide a prediction of one’s future behavior. Detect malicious and selfish entities.
Examples: E-commerce : risk estimation P2P : reducing free riding Mobile ad hoc networks : mitigating nodes selfish behavior

Wireless & Network Security 3 Kemal Akkaya
Trust Models Trust models entails collecting the information
necessary to establish a trust relationship and dynamically monitoring and adjusting the existing truth relationship.
Two models: Policy-based Trust
Based on access control Restricting access to resources according to application-defined policies PolicyMaker, Keynote, REFEREE
Reputation-based Trust a peer requesting a resource may evaluate its trust in the reliability of the
resource and the peer providing the resource Trust value assigned to a trust relationship is a function of the
combination of the peer’s global reputation SPORAS, HISTOS, XREP, NICE, DCRC/CORC, Beta, EigenTrust
Others: Social network-based Trust Utilize social relationships between peers when computing trust and
reputation values

Wireless & Network Security 4 Kemal Akkaya
Policy-based Trust

Wireless & Network Security 5 Kemal Akkaya
Policy-based Trust: virtual
Problems They do not provide a complete generic trust
management solution for all decentralized applications
Scalability

Wireless & Network Security 6 Kemal Akkaya
Reputation-based Trust Community of cooks (200 people) Need to interact with someone you don’t know,
To extablish trust: you ask your friends
– and friends of friends » ...
some recommendations are better than other you check the record (if any)
After success trust increases
p2p community of hackers (2000 people) Exchange programs & scripts
Need to interact with someone you don’t know, ...
Difference with concrete community: Larger, faster
Trust establishment has to be to some extent automatic

Wireless & Network Security 7 Kemal Akkaya
Challenges Trust metrics How to model and
compute trust Evaluating initial trust
value Combining evidences,
recommendations, reputation
Management of reputation data Secure & efficient
retrieval of reputation data
Automating trust based decision
Closing the circle: using experience as feedback

Wireless & Network Security 8 Kemal Akkaya
Reputation vs Policy-based Trust
open system (different security domains)
trust is a measure & changes in time
risk-based recommendation based
(NOT identity-based) peers are not
continuously available Some systems: PGP
TBD
open system (different security domains)
trust is boolean & less time-dependent
no risk rule (credential) based
(NOT identity-based) peers are not
continuously available Some systems: keynote,
Trust-X

Wireless & Network Security 9 Kemal Akkaya
Distributed Trust ModelsDistributed Trust Models Distributed Trust:
The representation of inputs to, and the process of making, trust decisions based on resources shared among multiple entities
Without Trust, either parties refuse to interact or require severe restrictions and complex controls – increased costs.
Trust is required for multiple entities to co-operate and share resources, and thus achieve some application value.
Conditional transitivity of trust if A trusts B & B trusts C then A trusts C if
B recommends its trust in C to A explicitly A trusts B as a recommender A can judge B’s recommendation and decide how much it will trust C,
irrespective of B’s trust in C
Will look at different models separately MANETs P2P Networks

Wireless & Network Security 10 Kemal Akkaya
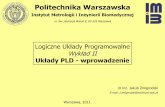
Comparison of TM Approaches
Approach Target Environ. Idea
AT&T labs(1996, 1998) PKI A lot like Access Control – Policy-based
Abdul-Rahman & Hailes (2000)
Virtual comm.Intro to Reputation-based Trust Models
& agents autonomy
Aberer & Despotovic (2001)
P2PAttempts distributed Storage of Trust info. – Reputation-based
CONFIDANT (2002) MANETAttempts incorporation of Detection & isolation of misbehavior
SECURE (2003)Ubiquitous roaming entities
Attempts Incorporation of risk model with Trust
hTrust(2004) MANETTrust Management & dispositional trust.
Detection & isolation of malicious recommenders.
McNamara et al. (2006) MANET Mobility introduced as a factor
STRUDEL (2006) CPDCombat Tragedy of the commons (Selfishness of Nodes)
MATE (2006) MANETAttempts integrated management of trust and risk (an element of dispositional trust).